 Effectively protect your applications availability against dangerous
Effectively protect your applications availability against dangerous
DDoS volumetric attacks.
Do not count losses, do not explain yourself to your clients.
Act professionally.
Effective protection
- Protection of the network against volumetric attacks
- Protection of your business processes
- Protection against financial losses and image detriment
- Scrubbing at the single service level instead of the entire IP address
Reliable, efficient operation
- Short response rime
- Automatic attack detection
- Elimination of the human error factor
- High-performance operator platform
Simple service management
- Service management from the Customer Zone level
- Smooth change of the protection scheme
- Online access to statistics and reports
- Incident notifications
Fast implementation
- Startup within 7 business days
- Dedicated project team
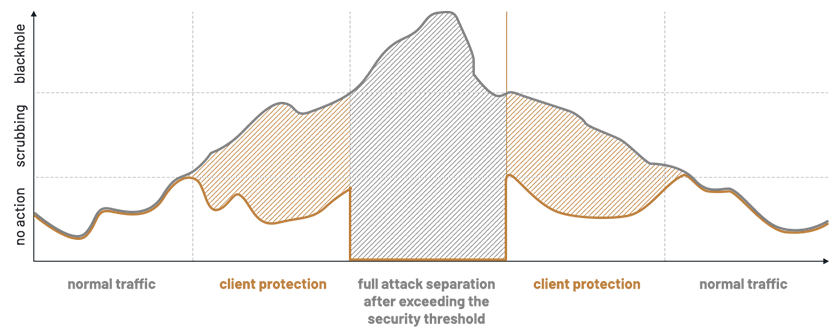
Flexible protection schemes
- Schemes with different sensitivity
- Thresholds determined by bps and pps parameters per target IP address
- Rules on scrubbing & blackholing
Compatibility
- It works natively with such services as: Atman Cloud, Business Internet,
Dedicated Servers
What is a DDoS attack
and why is it so dangerous for you?
DDoS (Distributed Denial of Service) is an attack carried out simultaneously from many computers and infected IoT devices (e.g. cameras) on computer systems of content and Internet service providers. It is specific because it cannot be distinguished from normal traffic by classic security systems. Such an attack consists in saturating client resources (e.g. Internet links), so, for security effectiveness purposes, it is critical to recognize and stop an attack at the infrastructure level of a telecommunications operator (e.g. Atman), which is capable of accepting and neutralizing an attack that is potentially very dangerous to the end client.
DDoS attacks have been around for a long time, but their form is getting more and more advanced. At present, such attack can be ordered by anyone, because their availability and price are not a barrier. This is one of the most common ways of maliciously blocking websites and web systems.
For an enterprise which provides online services, business losses related to overloaded servers and access links are not only limited to the inability to service clients during the attack. They also involve loss of confidence, financial losses, and damage to the company’s image, or a potential conflict within the organization. Protection against DDoS attacks has become as important as protection of IT resources against hackers and computer viruses.
Infrastructure and operation model
The Anti-DDoS solution is based on hardware components and application. Hardware components include Sensor and Scrubber, which are installed in Atman Data Centers.
Address pools are identified in the system which are to be observed. When the alarm threshold is exceeded, an anomaly is signaled.
The standard response to the anomaly is to run a filter, which means that the attacked host’s traffic is redirected to the scrubbers to mitigate the DDoS attack. The filtered traffic is sent back to the client by its primary link.
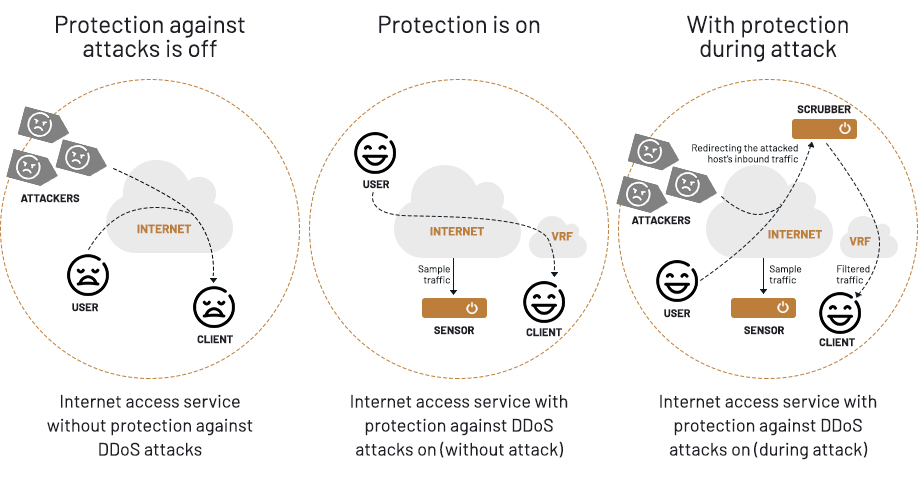
If the security thresholds are exceeded, the operator can activate black hole filtering to ensure that the client’s infrastructure will be 100% separated from the attack sources.


 The website uses cookies as described in our
The website uses cookies as described in our 